User Guide
Feed Detection Verification
You can quickly verify detection behavior by querying the IP addresses found in the C-TAS log menu as shown below.
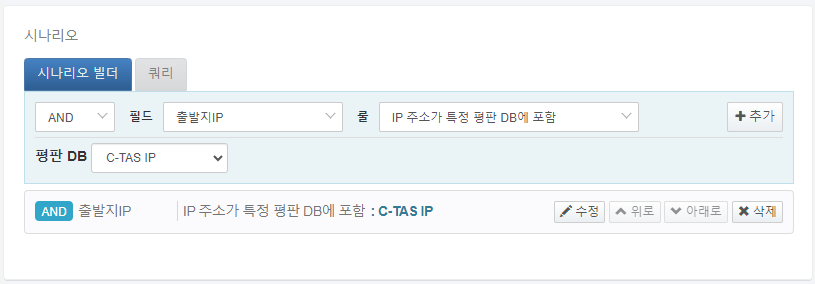
Real-time Scenario Configuration
For IP indicators of compromise, select the reputation DB inclusion rule for the source IP or destination IP in the scenario builder as shown below.
In general, rather than restricting detection to a specific reputation DB, it is recommended to select the IP address is included in reputation DB rule to enable detection across all IP indicator of compromise feeds.